‘Internet of Things’ an absolute goldmine for Big Brother, admits top US spy
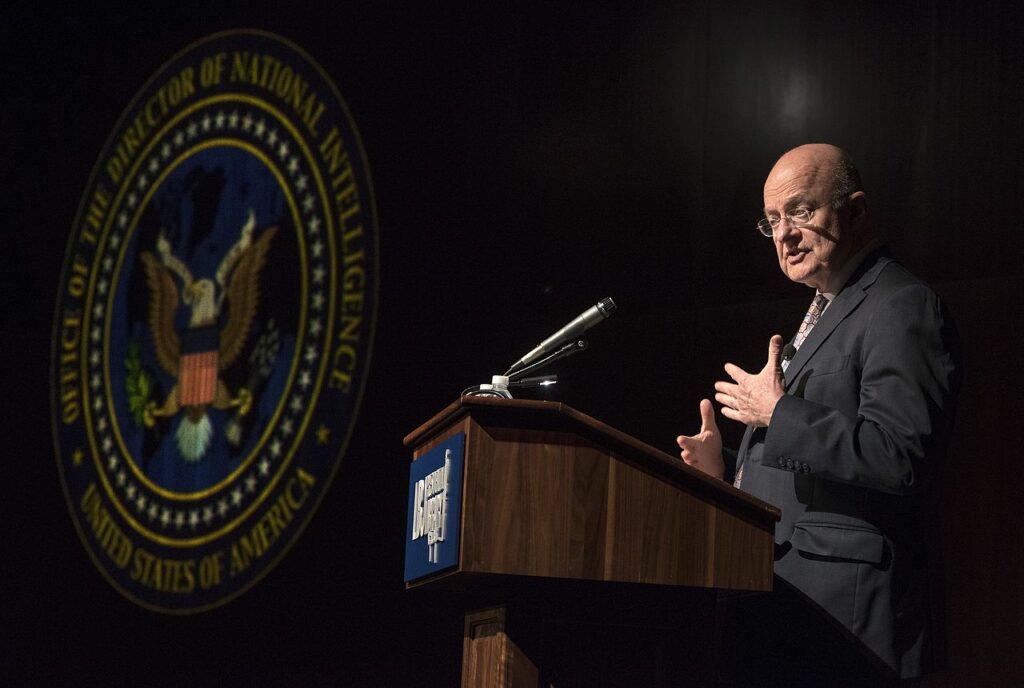
DNI’s James Clapper acknowledges “intelligence services might use the [web-connected home devices] for identification, surveillance, monitoring, location tracking, and targeting for recruitment.”
by Jon Queally
Sworn testimony delivered to the U.S. Congress by Director of National Intelligence James Clapper raised eyebrows on Tuesday as he acknowledged publicly for the first time that surveillance agencies are almost certain to exploit (if they aren’t already) the increasing number of web-connected devices – also known as the “Internet of Things”- as a way to keep tabs on the population in the coming years.
“In the future, intelligence services might use the [Internet of Things] for identification, surveillance, monitoring, location tracking, and targeting for recruitment, or to gain access to networks or user credentials,” Clapper said in his submitted testimony
In a piece at The Register—titled “We’re going to use your toothbrush to snoop on you, says US spy boss“—tech-security journalist Kieran McCarthy reports Clapper’s acknowledgement that the Internet of Things (IoT) is a “potential goldmine for surveillance” echoes “a similar conclusion reached by academics last week.” The testimony on Tuesday, McCarthy adds, follows “repeated warnings over the poor security standards included in smart-home products, even the most well-resourced and well-known. Recently, for example, the Ring doorbell* leaked people’s Wi-Fi keys.”
According to Guardian journalist Spencer Ackerman, Clapper’s admission about the surveillance potential of networked home devices—which also include wi-fi enabled smoke detectors, larger appliances, and entertainment systems—”is rare for a US official.” Not commonly discussed in public, Ackerman points to a 2012 speech by then CIA director David Petraeus who described the surveillance implications of such devices as “transformational… particularly to their effect on clandestine tradecraft.”
Though Clapper did “not specifically name any intelligence agency as involved in household-device surveillance”, reports Ackerman, “security experts examining the internet of things take as a given that the US and other surveillance services will intercept the signals the newly networked devices emit, much as they do with those from cellphones. Amateurs are already interested in easily compromised hardware; computer programmer John Matherly’s search engine Shodan indexes thousands of completely unsecured web-connected devices.”
As McCarthy adds:
“The data from IoT products can potentially be hugely valuable. Many include microphones and motion sensors, for example, such as new smart TVs, kids’ toys and voice-controlled products like Amazon’s Echo.
“It wasn’t just the internet of things that Clapper is worried/excited about. He also references that artificial intelligence is provided a similar risk/opportunity. By meddling with or anticipating the results of algorithms, a huge number of AI systems “are susceptible to a range of disruptive and deceptive tactics that might be difficult to anticipate or quickly understand.” On the flipside, however, they also “might create or enable further opportunities to disrupt or damage critical infrastructure or national security networks.”
And it’s not just the government spies that people worry about. In a post at ZDNet last year, Steve Ranger explores the many pitfalls and concerns presented by IoT, including the way in which private corporations will exploit the connectedness of new technologies.
“The IoT could be one of the purest outgrowths of late capitalism imaginable,” explained Ranger, “one that can packages your every waking minute into a product (and the sleeping ones too, of course — there’s many a way of making money out of the data you generate in your slumber).
“There’s a real danger that it could form part of the ongoing erosion and corporatisation of private spaces in the quest for profit. In a surveillance economy, privacy represents an opportunity for profit forgone.”
This article was originally published on Common Dreams and has been republished under a Creative Commons license.